Enhancing Server Security with Privileged Access Management (PAM) for Machine Identities
Error: No videos found.
Make sure this is a valid channel ID and that the channel has videos available on youtube.com.
The Future of PROTECTION
- Introduction to Security and AI
- Key Differences Between Traditional Cybersecurity ….
- How AI Reshapes the Digital Security and Risk….
- The Benefits of AI-Driven Security Across Industries
- Conclusion
- The Evolution of Cybersecurity
- Early Computing Technologies and Their Role in Shaping….
- Pivotal Moments in Cybersecurity Transformation….
- The Benefits of AI-Driven Evolution in Cybersecurity
- Conclusion
- The Role of AI in Threat Detection
- Challenges AI Faces in Identifying Novel Cyber Threats
- Differentiating Between Legitimate Threats and….
- Benefits of AI-Driven Threat Detection
- Conclusion
- Machine Learning Algorithms in Security
- Unsupervised Learning for Identifying Zero-Day Threats
- Deep Learning for Classifying and Prioritizing Security….
- Benefits of Machine Learning in Cybersecurity
- Conclusion
- AI and Cyber Attack Prevention
- Potential Pitfalls in Using AI for Proactive Cyberattack….
- Benefits of AI-Driven Cyberattack Prevention
- Challenges and Considerations
- Conclusion
- Privacy Concerns with AI in Security
- How AI in Cybersecurity Raises Concerns About….
- Measures to Ensure AI Systems Do Not Infringe on….
- Benefits of Privacy-Conscious AI in Cybersecurity
- Conclusion
- AI-Driven Security Automation
- How AI-Based Security Automation Improves Incident….
- Security Tasks Most Effectively Automated Using AI
- Benefits of AI-Driven Security Automation
- Conclusion
- AI in Identity and Access Management (IAM)
- Securing Privileged Access in Multi-Cloud and….
- AI’s Role in Managing Privilege Escalation Within….
- Benefits of AI in IAM
- Conclusion
- AI in Malware Detection and Mitigation
- Predicting Malware Behavior Before Activation:
- Limitations of AI in Detecting Advanced Persistent….
- Benefits of AI in Malware Detection and Mitigation
- Conclusion
- AI in Phishing Attack Prevention
- Adapting to Evolving Phishing Tactics
- Effective AI-Based Tools for Phishing Prevention…
- Challenges in Implementing AI for Phishing Prevention
- Conclusion
- The Ethics of AI in Cybersecurity
- Ethical Concerns in Deploying AI for Security….
- Guidelines to Prevent AI Systems From Being Exploited….
- Balancing Security and Ethics in AI Deployment
- Conclusion
- Deep Learning and Neural Networks in Security
- Advantages of Deep Learning and Neural Networks in….
- Strategies to Address Challenges
- Applications of Deep Learning in Cybersecurity
- Conclusion
- The Role of AI in Risk Assessment
- Accuracy of AI in Predicting Future Vulnerabilities….
- Benefits of AI in Risk Assessment
- Challenges and Considerations
- Conclusion
- AI and Cybersecurity Incident Response
- The Role of AI in Automating Incident Response….
- Benefits of AI in Incident Response
- Challenges in Implementing AI for Incident Response
- Conclusion
Chapter 15
- The Future of AI and Security
- Emerging AI Techniques That Could Revolutionize….
- Predictions for AI in Cybersecurity Over the Next….
- Conclusion
Chapter 16
- AI and Security in Cloud Computing
- How AI Contributes to Securing Cloud Infrastructure….
- Benefits of AI in Cloud Security
- Challenges in AI-Driven Cloud Security
- Conclusion
Chapter 17
- Cybersecurity AI Models and Bias
- Steps to Ensure AI Models in Cybersecurity Are Free….
- Can Bias in AI Security Systems Lead to Increased….
- Strategies to Mitigate Bias-Related Vulnerabilities
- Conclusion
Chapter 18
- AI for Security in the Internet of Things (IoT)
- How AI Enhances Security Monitoring in IoT….
- Challenges for AI-Driven IoT Security
- Practical Applications and Use Cases
- Conclusion
Chapter 19
- AI in Security Monitoring and Surveillance
- AI in Physical Security Monitoring
- Privacy Implications of AI-Driven Surveillance….
- The Future of AI in Security Monitoring and Surveillance
- Conclusion
Chapter 20
- The Intersection of AI and Ethical Hacking
- AI in Penetration Testing: Simulating Sophisticated….
- Advantages of AI in Vulnerability Scanning and….
- Challenges of AI in Ethical Hacking
- Conclusion
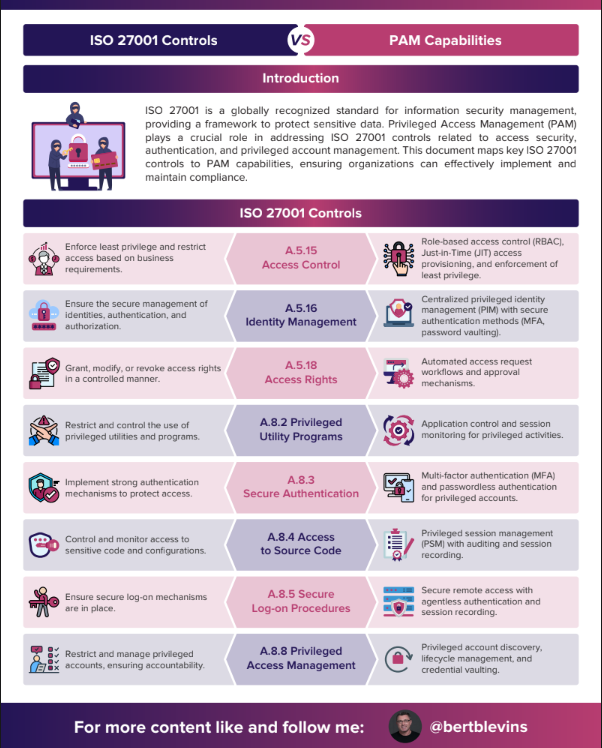
ISO 27001 Controls VS PAM Capabilities
Introduction
ISO 27001 is a globally recognized standard for information security management, providing a framework to protect sensitive data. Privileged Access Management (PAM) plays a crucial role in addressing ISO 27001 controls related to access security, authentication, and privileged account management. This document maps key ISO 27001 controls to PAM capabilities, ensuring organizations can effectively implement and
maintain compliance.
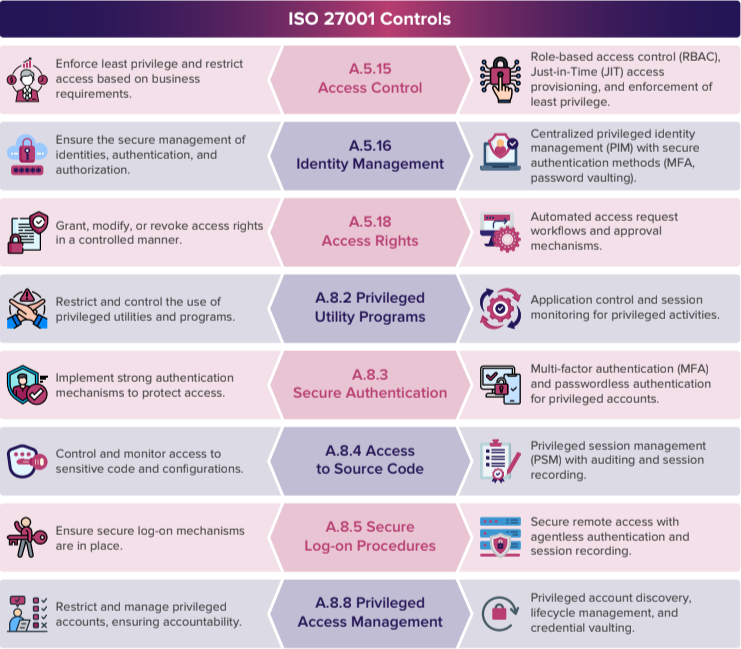
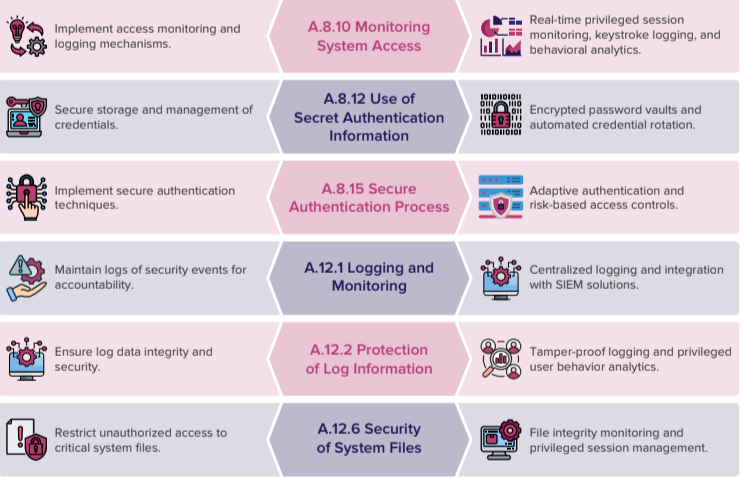
Conclusion
Implementing PAM solutions aligned with ISO 27001 controls helps organizations enhance their security posture, reduce attack surfaces, and ensure compliance. By integrating PAM capabilities, organizations can eectively manage privileged access, enforce least privilege, and maintain audit readiness.
Next Steps:
Conduct a PAM maturity assessment
aligned with ISO 27001.
Implement automated access
control mechanisms.
Establish continuous monitoring
and audit practices.
What Are Machine Identities?
Machine identities are the digital credentials—such as digital certificates, SSH keys, API tokens, and cryptographic keys—that authenticate machines within digital ecosystems. These identities allow servers, applications, IoT devices, containers, and other automated systems to securely communicate and prove their legitimacy in increasingly complex IT environments.
Why Securing Machine Identities Is Critical
As machines increasingly interact autonomously, protecting their identities is vital to prevent cyberattacks like impersonation, unauthorized access, and data breaches. Unsecured or mismanaged machine identities expose organizations to risk by enabling attackers to hijack communications, escalate privileges, and move laterally across networks. Robust machine identity security ensures trust, integrity, and confidentiality in machine-to-machine communication.
Ready to safeguard your machine identities?
Explore our advanced solutions, learn best practices, or request a personalized demo today.
Why Secure Machine Identities Matter
The rapid rise of automated machine-to-machine interactions has expanded the attack surface, making machine identities a prime target for cyber threats. Compromised certificates or keys can lead to devastating outcomes, including unauthorized data access, widespread breaches, and unchecked lateral movement within networks.
Additionally, stringent regulations such as GDPR, HIPAA, PCI-DSS, and NIST standards increasingly mandate secure management of machine identities, making compliance a key driver for organizations to adopt effective machine identity governance.
Why Secure Machine Identities Matter
- Digital Certificates (X.509), SSH Keys, API Keys, Cryptographic Tokens:
- Public Key Infrastructure (PKI):
- Certificate Lifecycle Management:
- Identity and Access Management (IAM) Integration:
Solutions & Features
- Automated Certificate and Key Lifecycle Management:
- Continuous Monitoring and Risk Assessment:
- Discovery Tools:
- DevOps, Cloud, and Security Platform Integrations:
- Alerting and Remediation Workflows:
Use Cases
- Securing TLS/SSL Certificates:
- Managing SSH Keys:
- Protecting Cloud-Native and Containerized Environments:
- IoT Device Authentication:
Industry Compliance & Standards
Effective machine identity management supports compliance with global and industry-specific regulations. Our solutions help you meet requirements set forth by GDPR, HIPAA, PCI-DSS, and adhere to frameworks like the NIST Cybersecurity Framework by enforcing rigorous control, auditability, and governance over machine credentials.
Customer Success Stories
Discover how organizations worldwide have leveraged our machine identity solutions to reduce security risks and achieve operational efficiencies.
“Since implementing automated machine identity management, we have eliminated certificate outages and significantly improved our security posture.” – IT Security Lead, Fortune 500 Company
Read more case studies demonstrating measurable benefits and reduced compliance burdens.
Educational Resources
Stay informed with our comprehensive resources:
- Blogs exploring machine identity security trends and emerging threats.
- Whitepapers outlining best practices for effective machine identity lifecycle management.
- Webinars featuring expert insights and product demonstrations.
- FAQs addressing common questions about machine identity risks and solutions
Technical & Integration Details
Our platform offers broad compatibility with existing enterprise technologies:
- Integration with PKI systems, IAM platforms, SIEMs, and orchestration tools.
- Robust API and SDK support for customized automation, reporting, and workflow management.


Understanding Machine Identities
The Role of PAM in Securing Machine Identities
Privileged Access Management (PAM) aims to monitor and manage access to sensitive data and critical systems. PAM solutions help organizations enforce the principle of least privilege, ensuring that only authorized machines can access specific resources. Here are key ways PAM enhances server machine identity security:

Centralized Credential Management
PAM systems centralize the management and storage of machine credentials, including SSH keys, API tokens, and certificates. By securing these credentials in a vault, PAM simplifies machine identity management and reduces the risk of unauthorized access. This centralization also facilitates credential rotation, revocation, or modification without disrupting services.

Automated Credential Rotation
Regularly rotating credentials is a best practice for managing machine identities. PAM systems automate this process, ensuring that machine identities are consistently updated with fresh, secure credentials. Automated rotation reduces administrative overhead for IT teams and lowers the risk of credential compromise.
Audit and Monitoring
PAM's comprehensive auditing and monitoring capabilities enable organizations to track and log all machine identity activities and access attempts. This visibility is crucial for detecting and responding to unauthorized access or suspicious behavior. Detailed logs and reports from PAM solutions help organizations comply with regulatory requirements and conduct forensic investigations if needed.
Enforcing Least Privilege
By implementing the principle of least privilege, PAM ensures that machine identities have only the minimum access necessary to perform their functions. This minimizes potential damage if a machine identity is compromised. PAM systems can dynamically adjust privileges based on the context of the request, further enhancing security.
Policy-Based Access Control
PAM allows organizations to define and enforce machine identity access policies. These policies specify which machines can access certain resources, under what conditions, and for how long. Policy-based access control ensures that access is consistently granted in line with organizational security policies.

Best Practices for Securing Machine
Identities with PAM
Error: No videos found.
Make sure this is a valid channel ID and that the channel has videos available on youtube.com.
Securing Machine Identities in Containerized Environments with Privileged Access Management (PAM)
The Complexity of Machine Identities in Containers
Ephemerality
Containers are short-lived, often created and destroyed within minutes.
Scalability
Containers can scale up and down dynamically based on demand.
Microservices Architecture
Containers frequently communicate with each other, necessitating robust authentication and authorization mechanism
Dynamic Workloads
The workloads running within containers can change rapidly, requiring adaptive security measures.
The Role of PAM in Containerized Environments
Centralized Credential Management
Automated Credential Rotation
Fine-Grained Access Control
Real-Time Monitoring and Auditing
Integration with Orchestration Platforms
Best Practices for Integrating PAM in Containerized Environments
Adopt a Zero-Trust Approach
Use Short-Lived Credentials
Enable Mutual TLS (mTLS)
Leverage Secrets Management Tools
Regularly Audit and Review Policies
Automate Security Enforcement
Error: No videos found.
Make sure this is a valid channel ID and that the channel has videos available on youtube.com.